TL;DR:
A user interface that brings together multiple pipelines to deliver full-stack visibility across cloud environments, exposing and correlating security risks at both the platform and operating system layers.
Overview
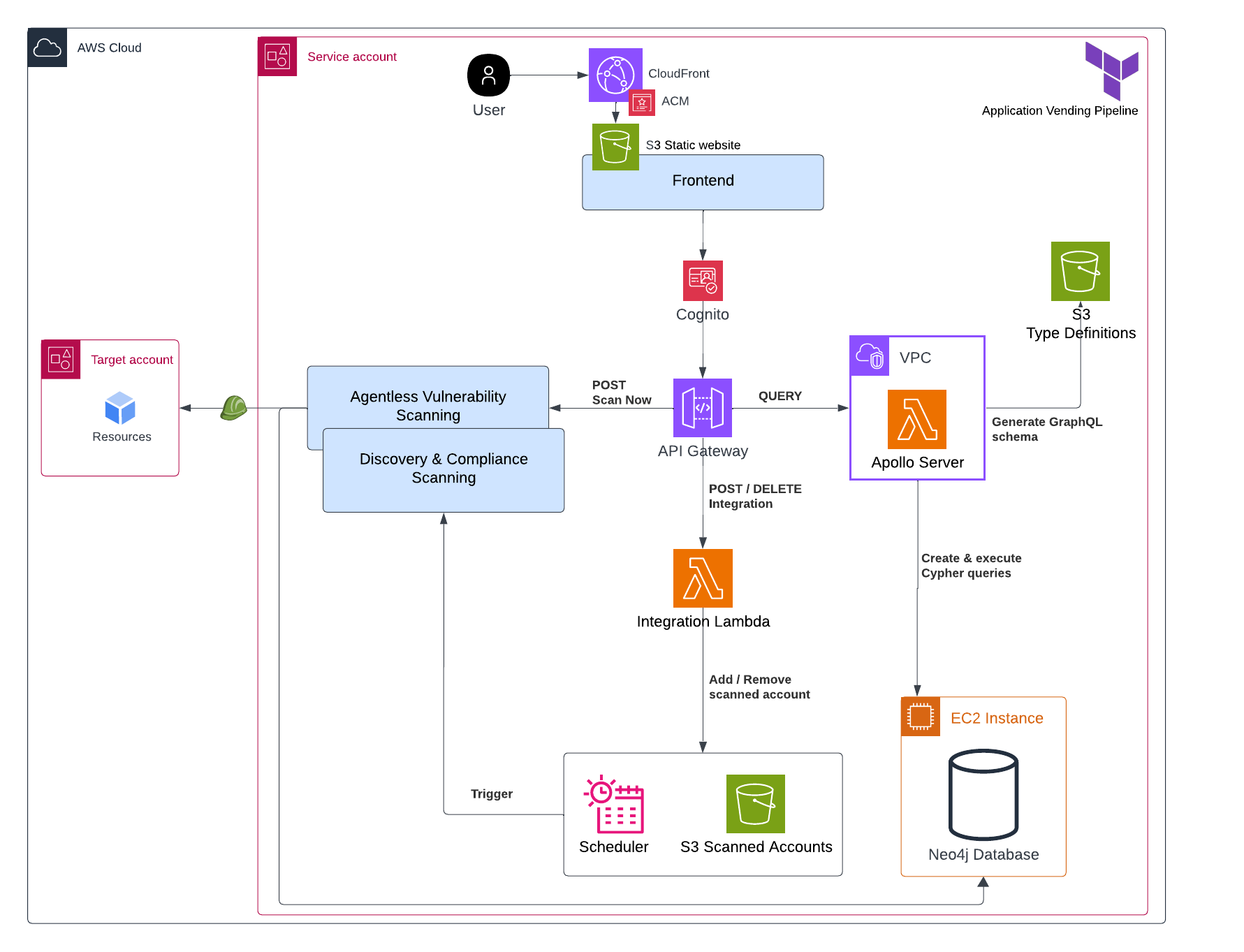
So far, Agentless Vulnerability Scanning, Discovery and Compliance Scanning, and Application Vending Pipeline have been explored individually.
This section introduces the final piece that brings them together into a cohesive CSPM application: the frontend and the orchestration glue.
The project
Backend
1. Website hosting
The platform user interface is written in NextJS and is hosted as a static website on S3. The build and deploy process is covered in Account Vending Pipeline.
Cloudfront fronts the S3 origin, using a custom domain managed through Route53 and an SSL certificate issued by Amazon Certificate Manager.
2. Authentication
Cognito provides user management for the platform. The Cognito Identity JavaScript SDK is used for user registration and authentication through the signUp and authenticateUser flows, removing the need to manage a separate database and user model.
3. Actions
API Gateway acts as the bridge between the frontend and backend. It validates Cognito-issued tokens before authorizing reqests to backend services.
For each module (compliance, discovery, vulnerability), three core requests are available:
- Scan now
- Invokes a Lambda function that initiates Agentless Vulnerability Scanning or Discovery & Compliance Scanning
- Add
- Remove
The Add and Remove requests invoke an integration Lambda responsible for creating or deleting an account’s schedule and S3 namespace.
A Query request is also available and covered below.
4. Data fetching
Two components are used to query the Neo4j database:
Neo4j GraphQL Library enables GraphQL access to Neo4j by generating an executable schema from statically supplied type definitions. These definitions are stored in S3.
Apollo Server runs on a VPC Lambda as the GraphQL API. It receives GQL queries and executes the resolvers generated by the library mentioned above. These resolvers transform GQL into Cypher, Neo4j’s native querying language, and execute it against the database.
Frontend
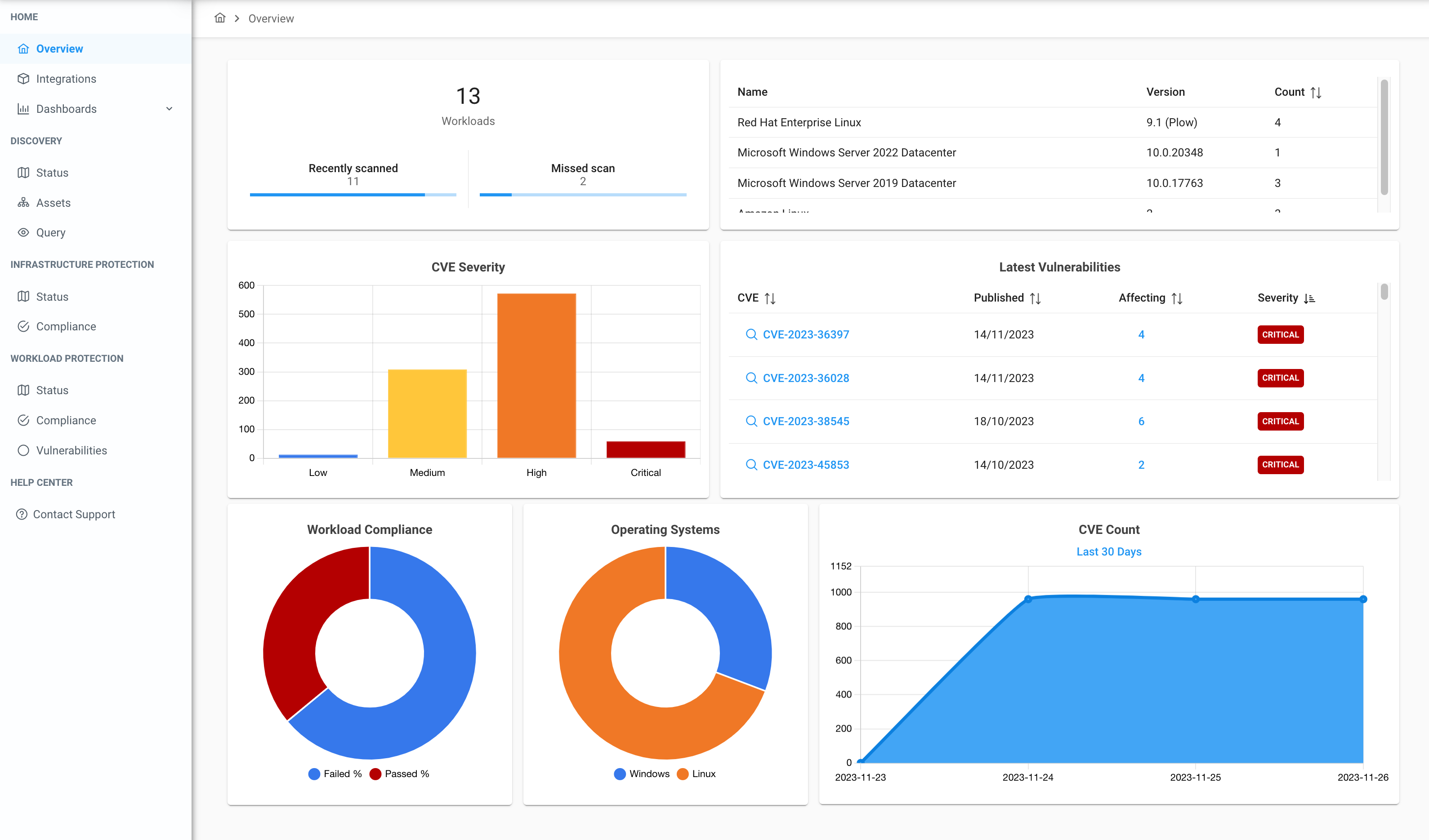
1. Dashboards
Multiple dashboards are available, offering visibility into onboarded accounts, compliance posture, and scanned services such as IAM, EC2, KMS, and others.
The Javascript code powering these dashboards is template-driven, allowing new dashboards to be created quickly through a JSON specification.
The dashboard shown below focuses on workload security at a high level.
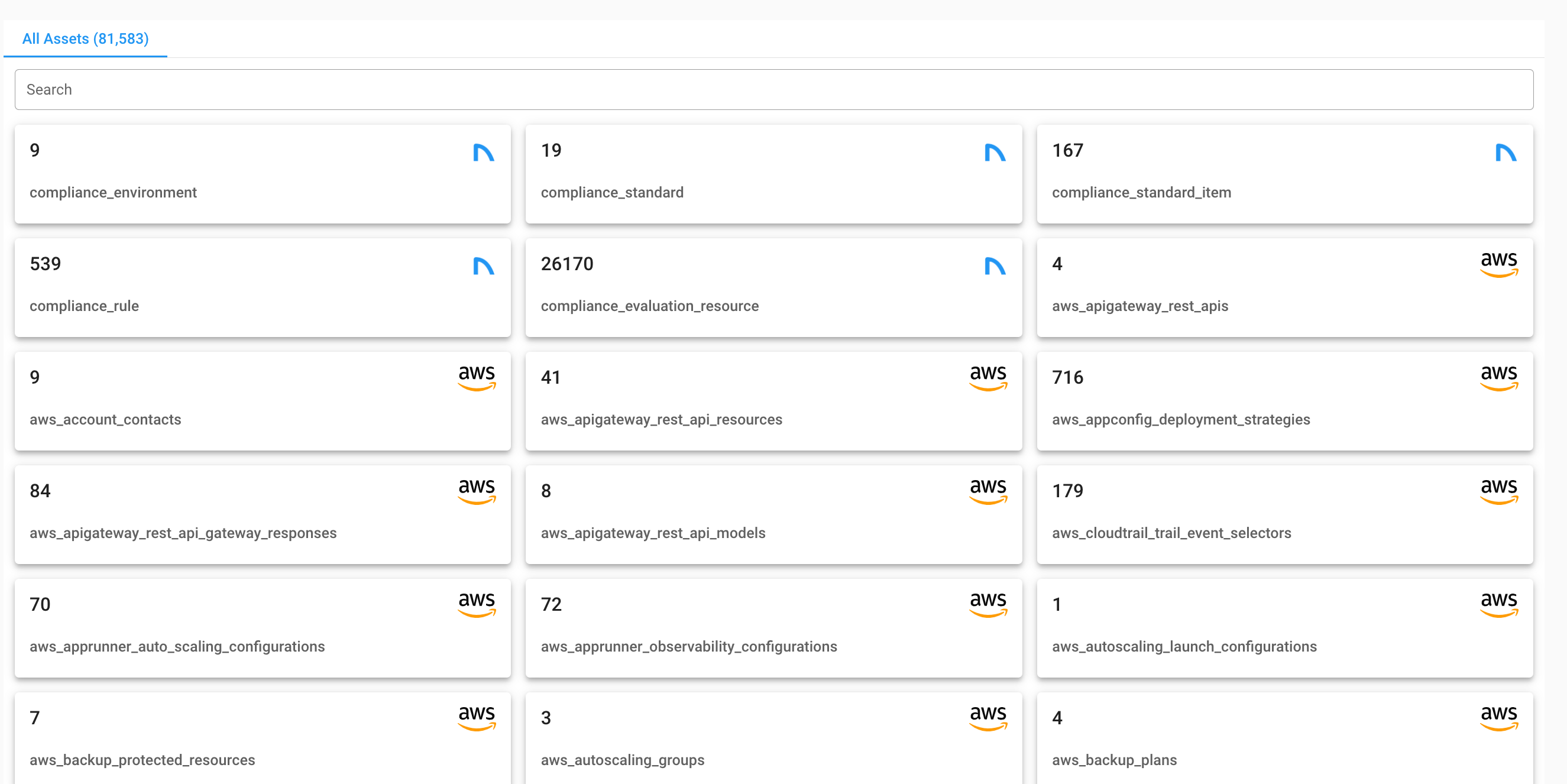
2. Discovery
A section which displays discovered entities across all onboarded accounts. Each tab is clickable, allowing deeper drill-down into specific details.
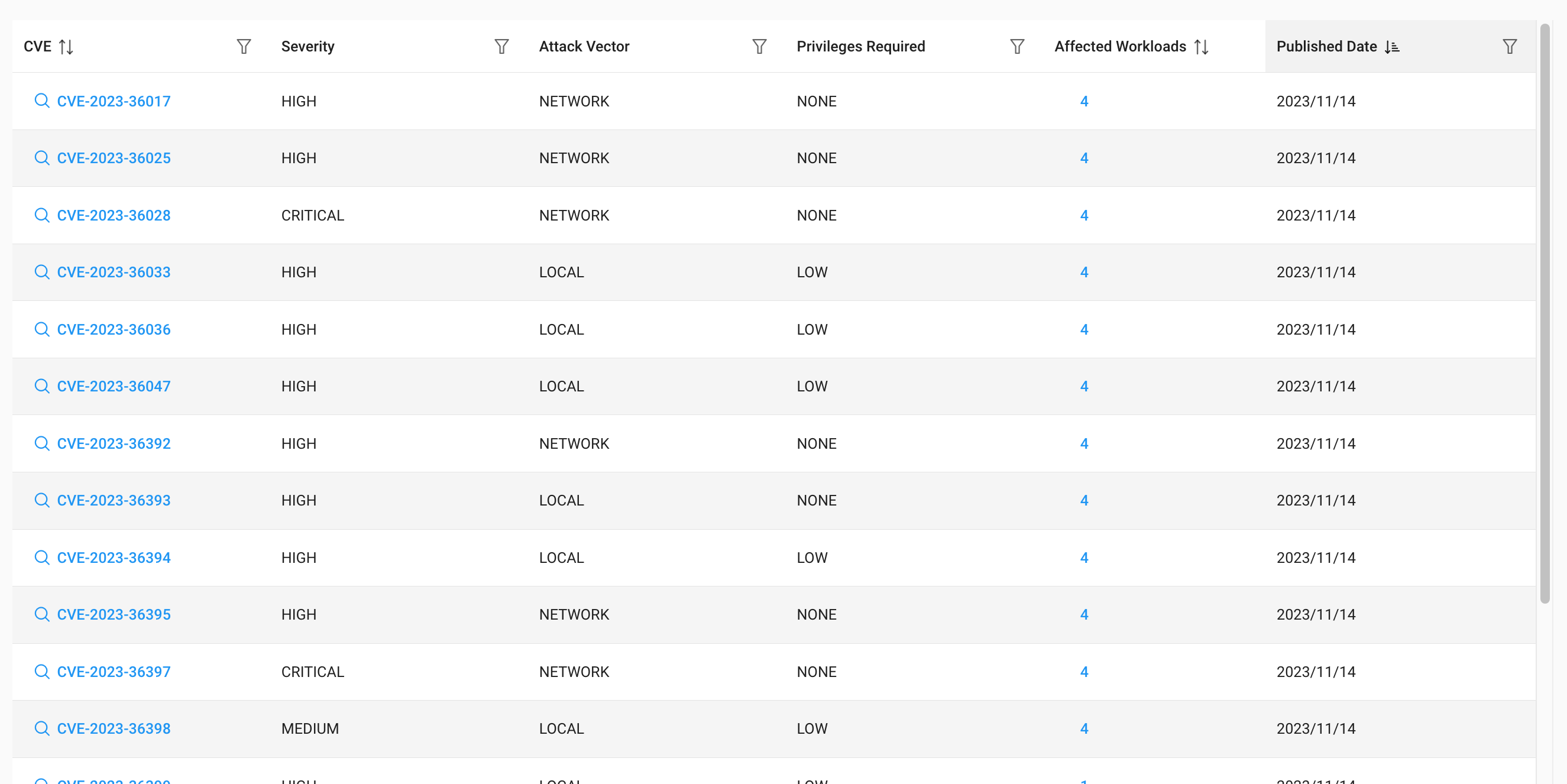
2. Vulnerabilities
A section listing all unique vulnerabilities identified across all onboarded accounts. Each item is clickable, providing additional details about the specific CVE, along with the workloads impacted by it.
3. Compliance
This module contains two separate sections, each focused on a different layer of visibility:
- Platform level
-
Displays results from infrastructure compliance scans, mapping cloud resource misconfigurations to specific controls within the selected standard. Users can choose from a list of available standards such as PCI DSS, CISA Cyber Essentials, and others, while filtering by scanned accounts.
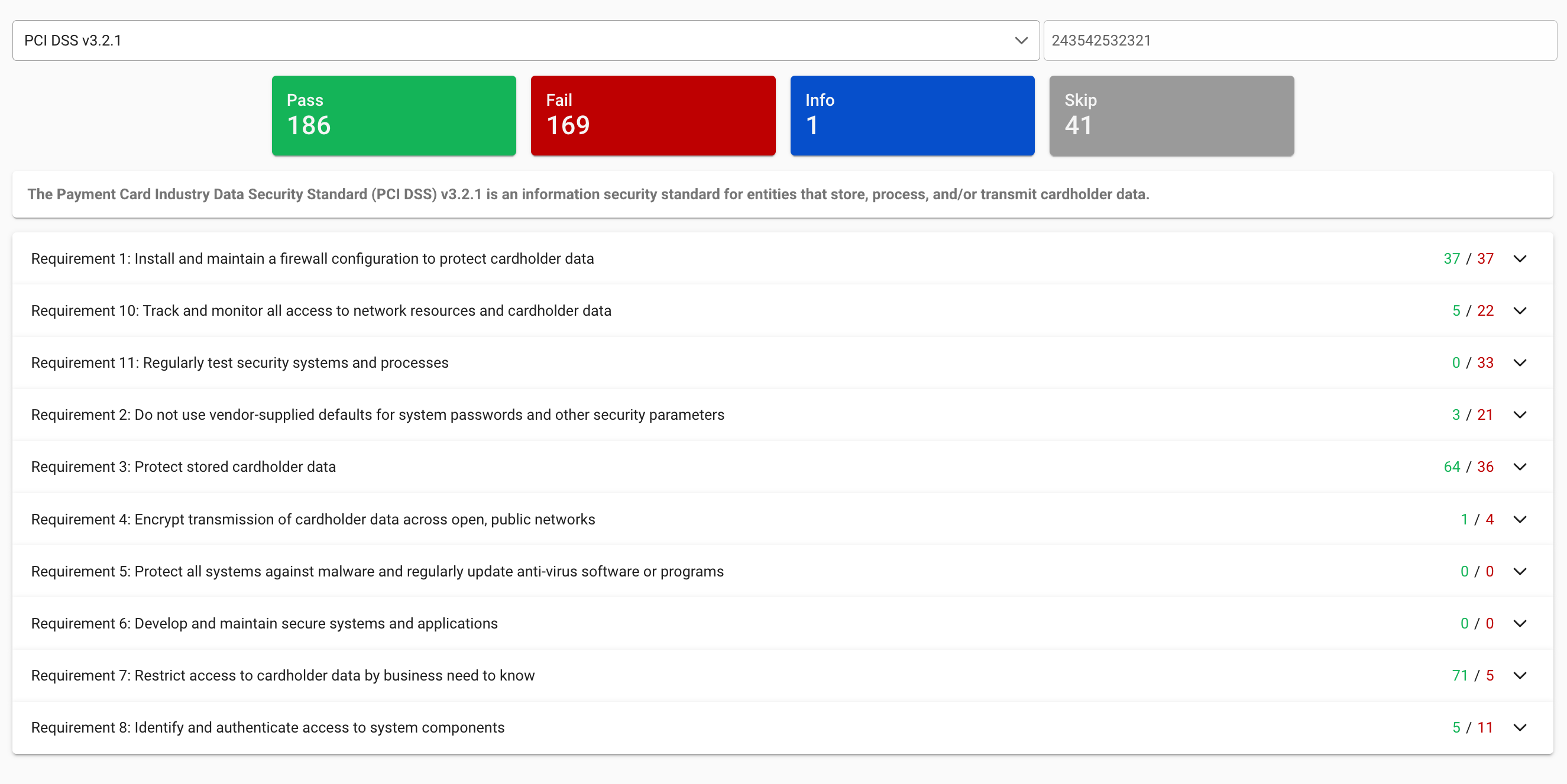
-
- OS level
-
Displays results from operating system compliance scans, mapping host misconfigurations against requirements from the Center for Internet Security (CIS) benchmark.
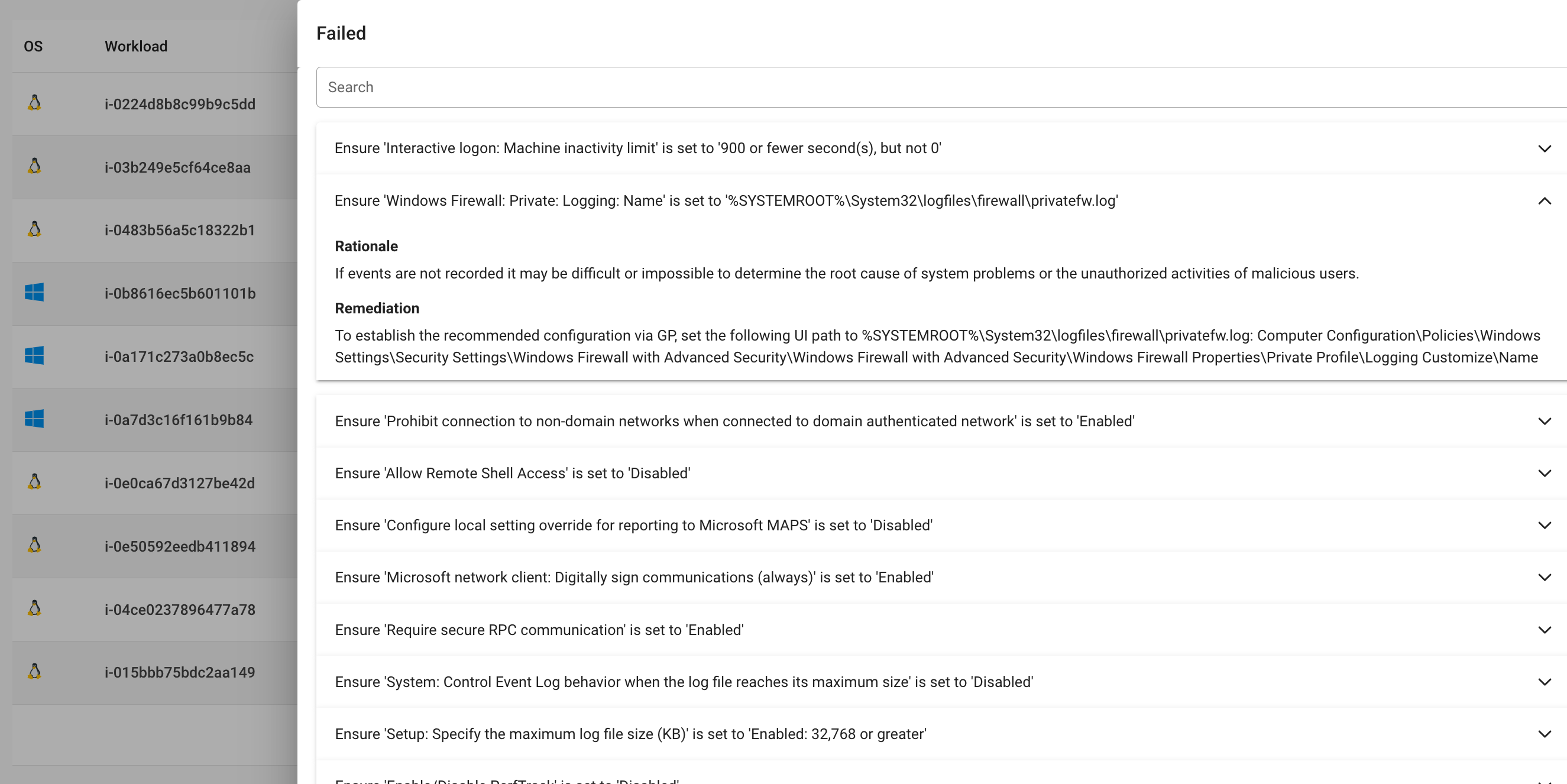
-
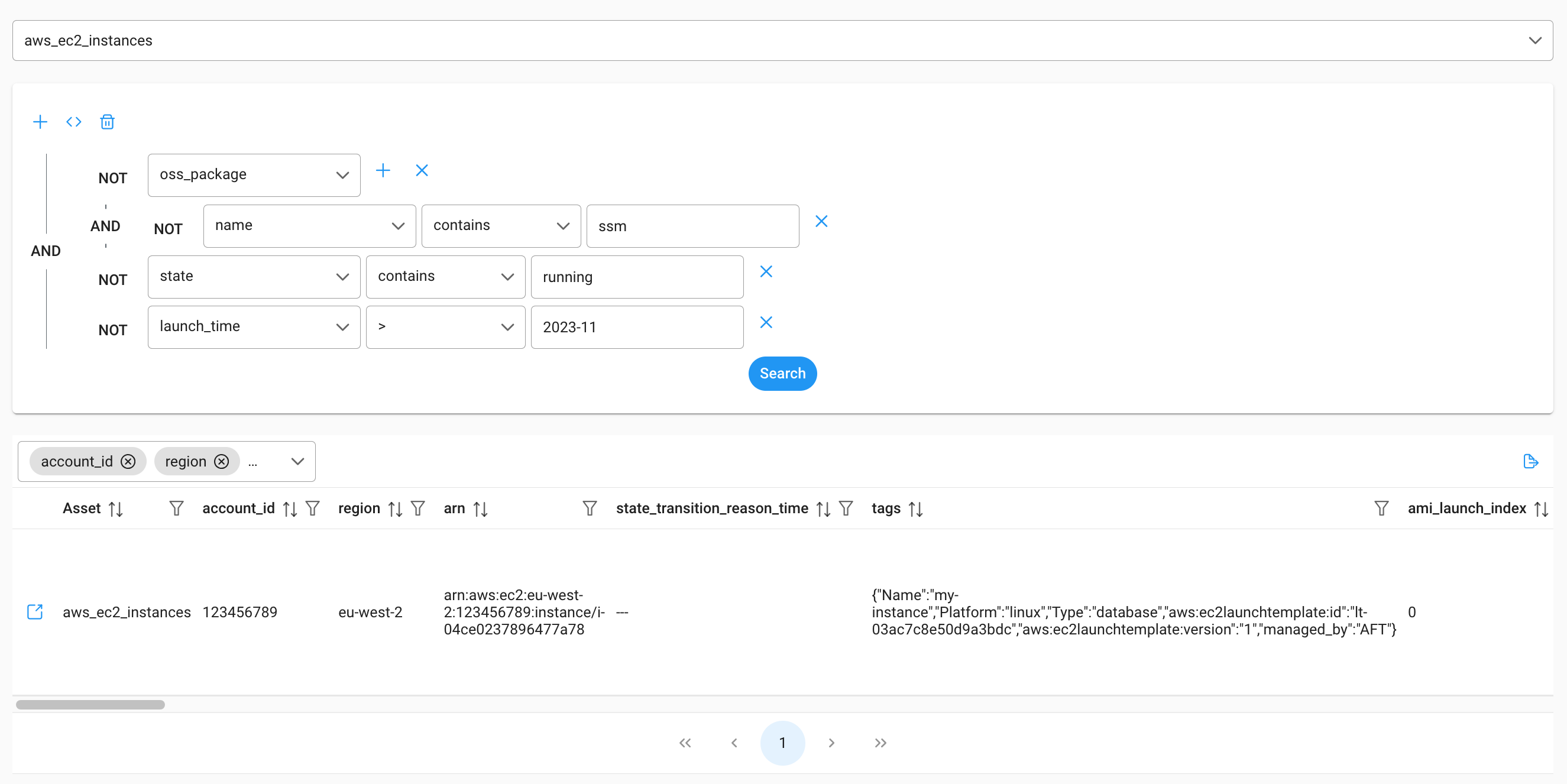
4. Query Builder
A single interface for querying all discovered resources, their configurations, compliance and vulnerabilities. It enables the creation of complex, cross-resource, even cross-account queries to derive meaningful conclusions.
On the frontend, uuser build queries through dropdown-based fields that define what they want to retrieve. On the backend, these inputs transformed into GraphQL queries, sent to Apollo Server, translated into Cypher, and executed against the database.
Result
By combining this NextJS application with Agentless Vulnerability Scanning, Discovery and Compliance Scanning, and Application Vending Pipeline, we have an excellent starting points for a fully fledged, self-hosted Cloud Security Posture Scanning platform, provisioned and managed entirely through infrastructure as code.
